The Analysis of Effect of Currency Exposure on Revenue
Question 1
- Frame the issue. Why is Brenzel Concerned by the current exchange rate fluctuation?
Because the company has a large amount of U.S. dollar accounts receivable, but the company’s basic currency is Canadian dollars. If in the future the Canadian dollar strengthens and the U.S. dollar falls, the company will bear the losses caused by this part of the exchange rate fluctuation.
Question 2
Which vehicles does Acpana have at its disposal for hedging? Assume Acpana will need to transfer $200,000 US dollars to Canadian dollars on a regular basis, calculate the impact of these different hedging strategies against a naked position at:
- 1 Cdn $ =1 US $;
- 1 Cdn $ = 0.90 US $;
- 1 Cdn $ = 1.10 US $.
Generally speaking, the tools for hedging can choose to buy Canadian dollar forward contracts or buy Canadian dollar options. The former can lock in the amount of Canadian dollars that will be exchanged for U.S. dollars in the future, and the latter can exercise the income in U.S. dollars after the Canadian dollar appreciates.
Although selling U.S. dollar options can make a profit when the Canadian dollar rises , there is a limit on the profit. Assuming that the same amount of options are sold, if the exchange rate exceeds ask, the rise cannot completely hedge against the Canadian dollar rise. In general, selling options is not a hedging to reduce risk, so in this case only data comparison is provided, not considered as a choice.
Different vehicles’ data refered from original paper.
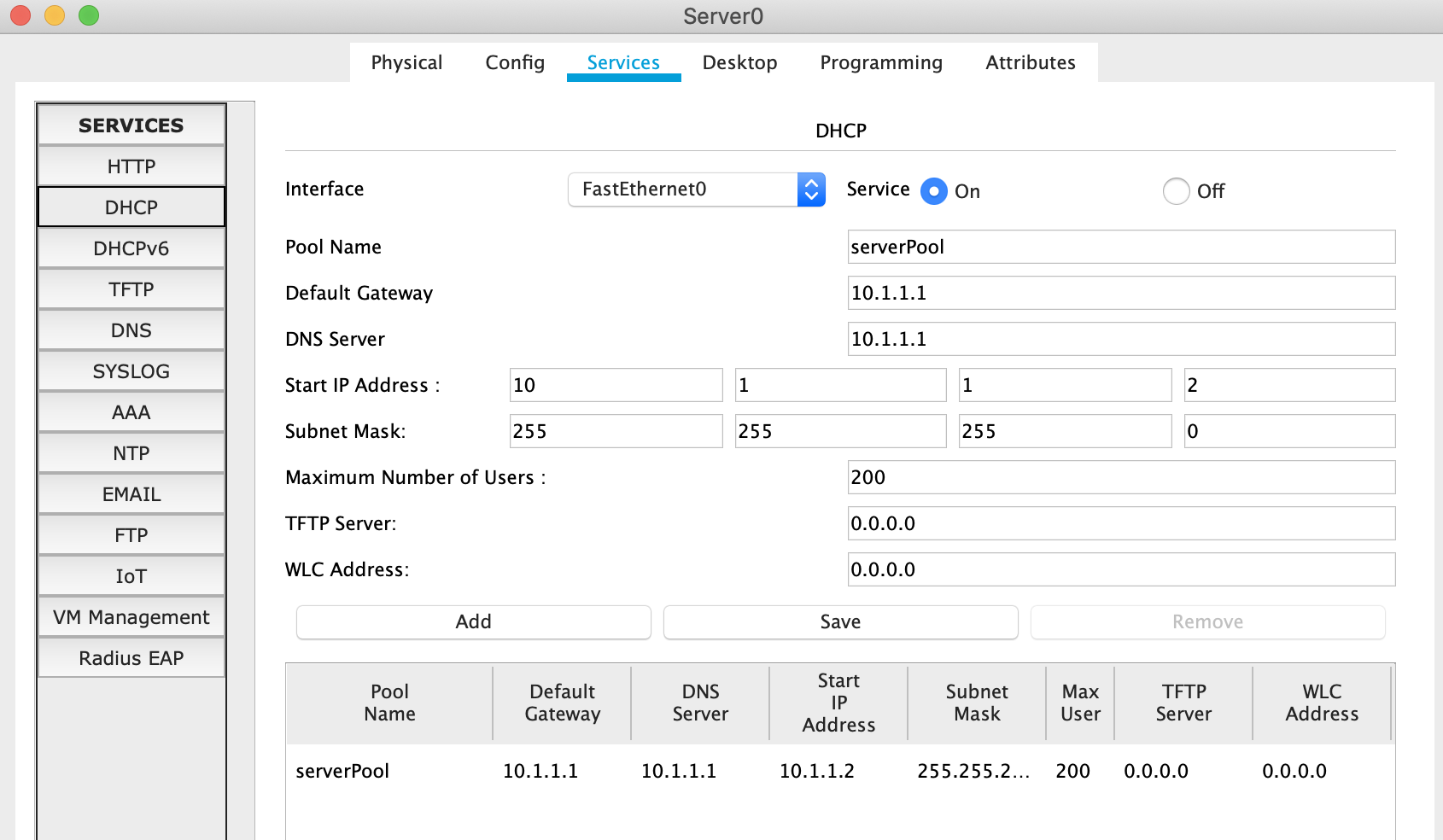
forward contract quotations
Spot 0.9731
| Period |
Ask |
| 1 Month |
0.97374 |
| 3 Month |
0.97510 |
| 6 Month |
0.97765 |
| 9 Month |
0.98052 |
| 1 Year |
0.98385 |
options quotations
Spot 0.9731
| Call Option |
|
|
Put Option |
|
|
| MM/DD/YY |
Strike |
Ask |
MM/YY |
Strike |
Ask |
| 04/01/11 |
0.97374 |
0.9334% |
04/01/11 |
0.97374 |
0.9334% |
| 06/02/11 |
0.97510 |
1.7150% |
06/02/11 |
0.97510 |
1.7150% |
| 09/05/11 |
0.97765 |
2.6023% |
09/05/11 |
0.97765 |
2.6023% |
| 12/02/11 |
0.98052 |
3.2584% |
12/02/11 |
0.98052 |
3.2584% |
| 03/02/12 |
0.98385 |
3.8363% |
03/02/12 |
0.98385 |
3.8363% |
Now we can compare the following three scenarios with the 200,000 U.S. dollar income receivable in Canadian dollars after one month of different exchange rates:
| exchange rate after 1 month |
do nothing |
sell US dollar contract |
buy CAD call option |
sell CAD put option |
| 1 Cdn $ =1 US $ |
200,000 |
1947480.00 |
1981332.00 |
1965657.78 |
| 1 Cdn $ = 0.90 US $ |
222,222.2 |
1947480.00 |
2201480.00 |
1965657.78 |
| 1 Cdn $ = 1.10 US |
181,818.2 |
1947480.00 |
1929302.22 |
1835152.73 |
It can be seen that while the call option maintains the ability to resist risks, it also has a certain profit margin.
Question 3
- Should Schenkel recommend Acpana hedge its position in Canadian dollars? Why or why not? If you think he should recommend a hedge, which vehicle should he recommend?
Let us first examine the yield curve of the above four processing methods from 0.9 to 1.1 on CND/USD. One-year futures and options expiring on 03/02/12 are used as the data benchmark.

It can be seen that in the next year, if the U.S. dollar rises sharply, it is optimal not to take any measures, and if the U.S. dollar plummets, it is optimal to sell forward dollar contracts.
However, it must be noted that no matter what kind of situation, the purchase option will not deviate too much from the optimal solution.
According to the forecast of the Economist Intelligence Unit given in the question in 2011, CAD/USD=0.98, that is, USD/CAD=1.0204, it can be seen that the sell put option is the optimal, and secondly, choosing to do nothing is the optimal solution.
But I think these two schemes are not hedging schemes.If the exchange rate drops to around 0.9, the loss will be larger, and as the exchange rate drops, the loss will change linearly.
Therefore, I would recommend the use of forward contracts, because this method is the most effective in combating risks.
Question 4
- Does the Economist Business Unit’s forecast that the Canadian dollar will finish the year at parity to the US dollar affect your decision to hedge?
Investigate the income of different monthly hedging products in the form of images:

In the case of USD/CAD=1, in products less than 6 months old, options are better than contracts, but in most cases it is still optimal to do nothing. But this does not affect my opinion, I still It is recommended to use forward contracts.
Summarize
Although in most cases, especially when the U.S. dollar is bullish, doing nothing is optimal, but in order to combat unknown risks, it is best to buy a certain amount of forward contracts to reduce the overall risk.